Machine Learning for RF Information Leakage Characterization in Low Cost Bluetooth Implementation
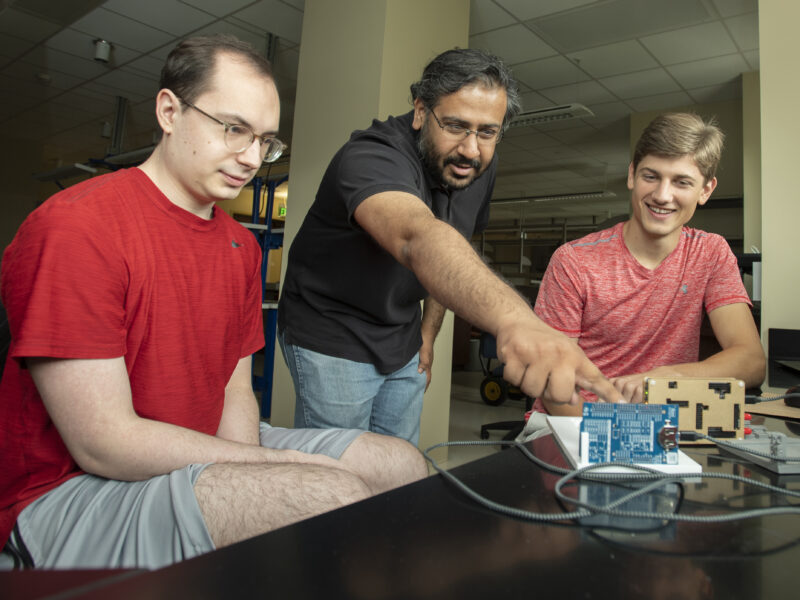
Principal Investigator: Professor Joshi
AWaRE REU Researcher: Colton Kammes, University of Notre Dame
Other Contributors: Mark Horeni and Tanner Waltz
Project Summary:
Due to tight on-die integration in low-cost, low-power wireless modules, digital and mixed-signal subsystems are often placed very close to each other. Noise coupling from the digital system is often indicative of the computations being performed and thus leaks information to the outside world. We would like to characterize this leakage and see what can we infer about the computations occurring inside the chip using only the signals leaking outside.
Finding:
System-on-Chips (SoCs) are integrated circuits that integrate multiple components of a computer. These devices are typically used in IoT and Smartphone applications and typically have radios in close proximity to the other components such as the processor and memory. Due to the proximity, CPU and Memory activity can propogate through the radio and leak data wirelessly through RF communications. When encryption (such as AES-128) is occurring on the chip, leakage is transmitted which can be used to determine the encryption key through template attack algorithms like canonical correlation analysis. Such algorithms require many traces to attack a single key, but a Multi-Layer Perceptron (MLP) can attack multiple keys with fewer traces. To train the MLP, a large, clean, and consistent dataset must be collected. After training, an MLP can collect a single trace from a target and recover information such as an encryption key. Single trace MLP attacks are a vast improvement to classic algorithms as they are faster and require significantly less data at the time of attack.

